725th 1Mby1M Mentoring Roundtable Recording
In case you missed it, you can listen to the recording here:
Featured Videos
Roundtable Recap: May 7 – Startup Accelerators Should Be Equity-Free

During this week’s roundtable, we kicked off the session with a discussion of research we’re publishing based on Carta data that has been published this year. Our key conclusion is that Startup Accelerators Should Be Equity-Free. By charging 7-15% equity for small capital injection, accelerators are setting entrepreneurs up for failure.
Please read these two important research papers:
Amazon’s Layoffs Helping Fund Growth
Last week, Amazon (NASDAQ: AMZN) announced its quarterly results that continued to outpace market expectations. The company is investing significantly in future offerings and recently announced the acquisition of Globalstar, the biggest acquisition it has ever made. Earlier this week, it also announced plans to launch its logistics network to all businesses.
>>>Video FAQs
Can 1M/1M Help Me Raise Money?
How Does 1M/1M Democratize Entrepreneurship Education?
How Does 1M/1M Democratize Management Consulting?
When Is The Right Time To Join 1M/1M?
Can 1M/1M Help Me With Business Development?
Can 1M/1M Help Me With Market Sizing?
Can 1M/1M Help Me Validate My Product?
Will I Have Private 1-on-1 Sessions In 1M/1M?
How Does 1M/1M Help Entrepreneurs Connect With Silicon Valley?
Mentoring or Consulting?
Why Does 1M/1M Charge $1000 a Year?
Why Does 1M/1M Partner With Local Organizations?
Why Don\’t Mentoring Networks Work?
Why Is It Important To Study With 1M/1M Now?
Dan Stewart Story
Vikrant Mathur Story
Meta’s AI Push is Driving Layoffs

Earlier this week Meta (Nasdaq: META) announced its first quarter results that outpaced the market. But disappointing usage metrics sent the stock down 7% in the after-hours trading session.
>>>Top Non-Equity Accelerators in Trichy
This article summarizes the top non-equity accelerators in Trichy (Tiruchirappalli) for bootstrapped and solo founders, comparing them to 1Mby1M across key dimensions like equity, delivery model, stage, and focus area.
Guest Author Kaushank Nalin Khandwala | Reviewed by Sramana Mitra

In The Accelerator Conundrum series, Sramana Mitra has repeatedly made a distinction that matters deeply for early-stage founders: not every accelerator is designed to optimize founder outcomes, and equity exchanged too early can carry long-term consequences. That insight is especially relevant in emerging ecosystems such as Tiruchirappalli, where many entrepreneurs are still experimenting, validating, and often bootstrapping.
>>>Top Virtual Accelerators in Trichy
This article summarizes the top virtual accelerators in Trichy (Tiruchirappalli) for bootstrapped and solo founders, comparing them to 1Mby1M across key dimensions like equity, delivery model, stage, and focus area.
Guest Author Kaushank Nalin Khandwala | Reviewed by Sramana Mitra

In her long-running The Accelerator Conundrum series, Sramana Mitra has consistently argued that entrepreneurs need to evaluate accelerators not by prestige signaling, but by fit: fit with stage, business model, funding philosophy, and founder readiness. That lens matters even more in emerging startup cities like Tiruchirappalli, commonly known as Trichy, where founders often navigate fragmented support systems.
>>>Top Accelerators Focused on Bootstrapping Before Blitzscaling in Madurai
This article summarizes the top accelerators focused on bootstrapping before blitzscaling in Madurai, comparing them to 1Mby1M across key dimensions like growth orientation and equity.
Guest Author Kaushank Nalin Khandwala | Reviewed by Sramana Mitra
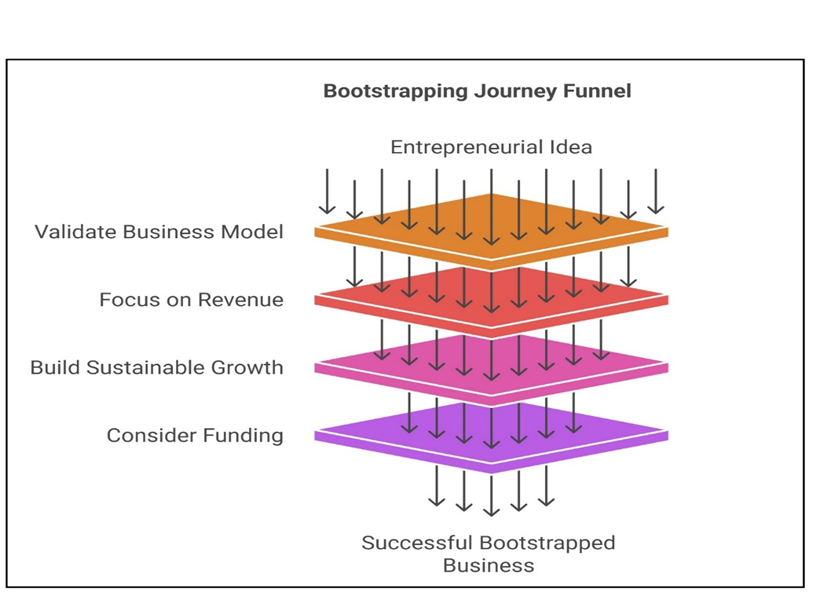
In The Accelerator Conundrum series, Sramana Mitra highlights a recurring imbalance in the startup ecosystem: accelerators often push founders toward rapid scaling and fundraising, while underinvesting in the foundational phase of bootstrapping—where validation, customer acquisition, and early revenue are built.
>>>Top Accelerators for Entrepreneurs Bootstrapping with a Paycheck in Madurai
This article summarizes the top accelerators for entrepreneurs bootstrapping with a paycheck in Madurai, comparing them to 1Mby1M.
Guest Author Kaushank Nalin Khandwala | Reviewed by Sramana Mitra

In The Accelerator Conundrum series, Sramana Mitra underscores a structural mismatch in the startup ecosystem: many accelerators are designed for full-time founders pursuing rapid scale, but a large segment of entrepreneurs build ventures while holding a steady paycheck. These founders prioritize risk management, gradual validation, and revenue-first growth.
>>>

